With an increasing focus on the resilience of organizations in today’s turbulent world many businesses are asking the question ‘who really controls our business-critical applications?’ On the surface, the answer should be clear: the business. But we should ask ourselves – is this really the case?
Who is really in control?
Every application runs on a computer or computers. That is the case even if the application runs in virtualised, containerised or even entirely server-less environment. The one who controls access to the computer has the ultimate control. There are various degrees of access different entities can have to the computers that run your application. Depending on where your application runs, different people will have physical access to servers. These may be people from your organization if you run your own data centers, or they may be from an entirely different company in an entirely different country that you contract to provide your infrastructure. Sometimes you may not even know where the servers are and may have no influence where and how your application is run.
The one who controls access to the computer has the ultimate control.
The next level up from physical access to the servers running your application would be access to the software infrastructure (server management, virtualization management etc.) that runs them. That would be the people who manage your datacenter or cloud infrastructure (like the employees of AWS/Amazon or Azure/Microsoft). People with access to this software backbone of your outsourced infrastructure may have the ability to shutter parts of it for operational or other reasons that may not have anything to do with how you use the application and may impact your access and therefore your business.
If you use Software as a Service (SaaS), then you also need to take into account your software vendor who has the ability to stop your access to the software, even though the infrastructure may still be running.
There are also a number of indirect factors outside of your control that can stop you from using your apps – for example, how reliable is your infrastructure provider’s electricity supply, their internet connection, or their hardware? Visibility from the client’s side is limited other than assurances of redundancy.
On-premise v Outsourced infrastructure v Software as a Service
Any business application will be deployed in one of these three ways – each with a different degree of control you can exert over it.
On-premise – You own the hardware and control access to the datacentre where the hardware is located.
Outsourced infrastructure (IaaS, PaaS) – You pay for the use of IT infrastructure that is owned and controlled by someone else (e.g. AWS, Azure).
Software as a Service (SaaS) – You pay for the use of the business application, regardless of what IT infrastructure it uses. The very large SaaS providers own their infrastructure; most SaaS providers use outsourced infrastructure providers to run their apps.
We need to note that each of these three options has a different cost structure (CapEx v OpEx, fixed costs v variable costs), different demands for organizational expertise (e.g. less IT expertise needed if all your apps are run as SaaS) and different degrees of flexibility (e.g. you won’t build your own datacentre overnight, but you can spin up a number of servers on AWS within minutes).
Ultimately, on-premise deployments give you the most control and SaaS deployments give you the least control.
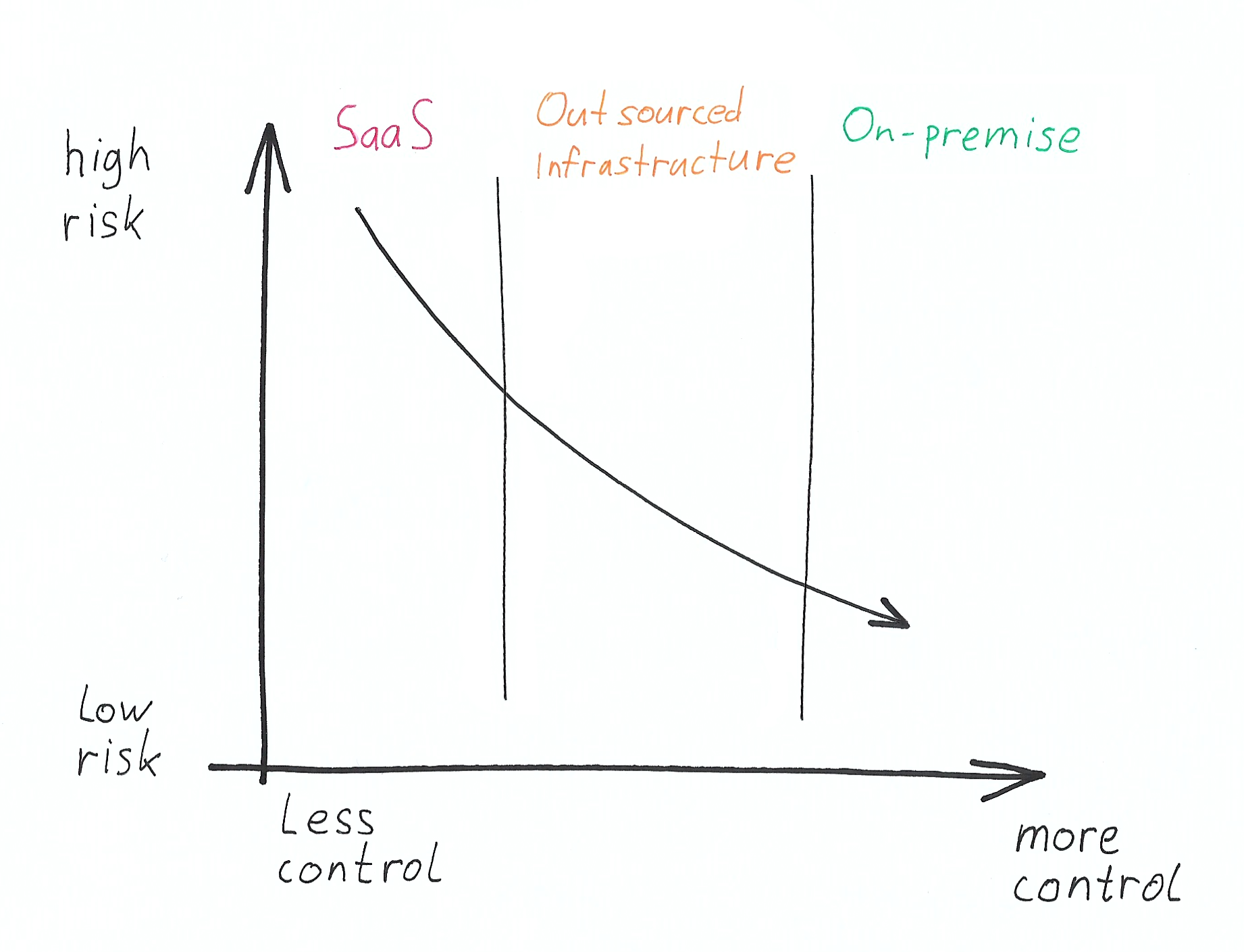
Overall, you need to balance the degree of actual control you have over the applications that enable your business to run, with the cost of maintaining that control to a useful degree – versus the risk of being impacted by negative events outside your control.
You pay for control. Control might pay back.
In terms of how much you pay for maintaining control and having a low level of risk of someone pulling the plug on your applications, the cost will largely depend on how much utilization you can achieve in the infrastructure you need. If you’re a business of about 100 people, it’s less likely that you can justify the building and running of your own datacenter, unless you’re highly specialised. However, for large companies who need to have full control of their business-critical applications, this is likely to be an interesting proposition and one that should cause you to pause for thought. Outsourced infrastructure and SaaS providers deliver a lot of their value from high utilisation of the server resources and the economies of scale. If you’re big enough to achieve high-enough utilization and scale, gaining more control can become a cash-positive endeavour.
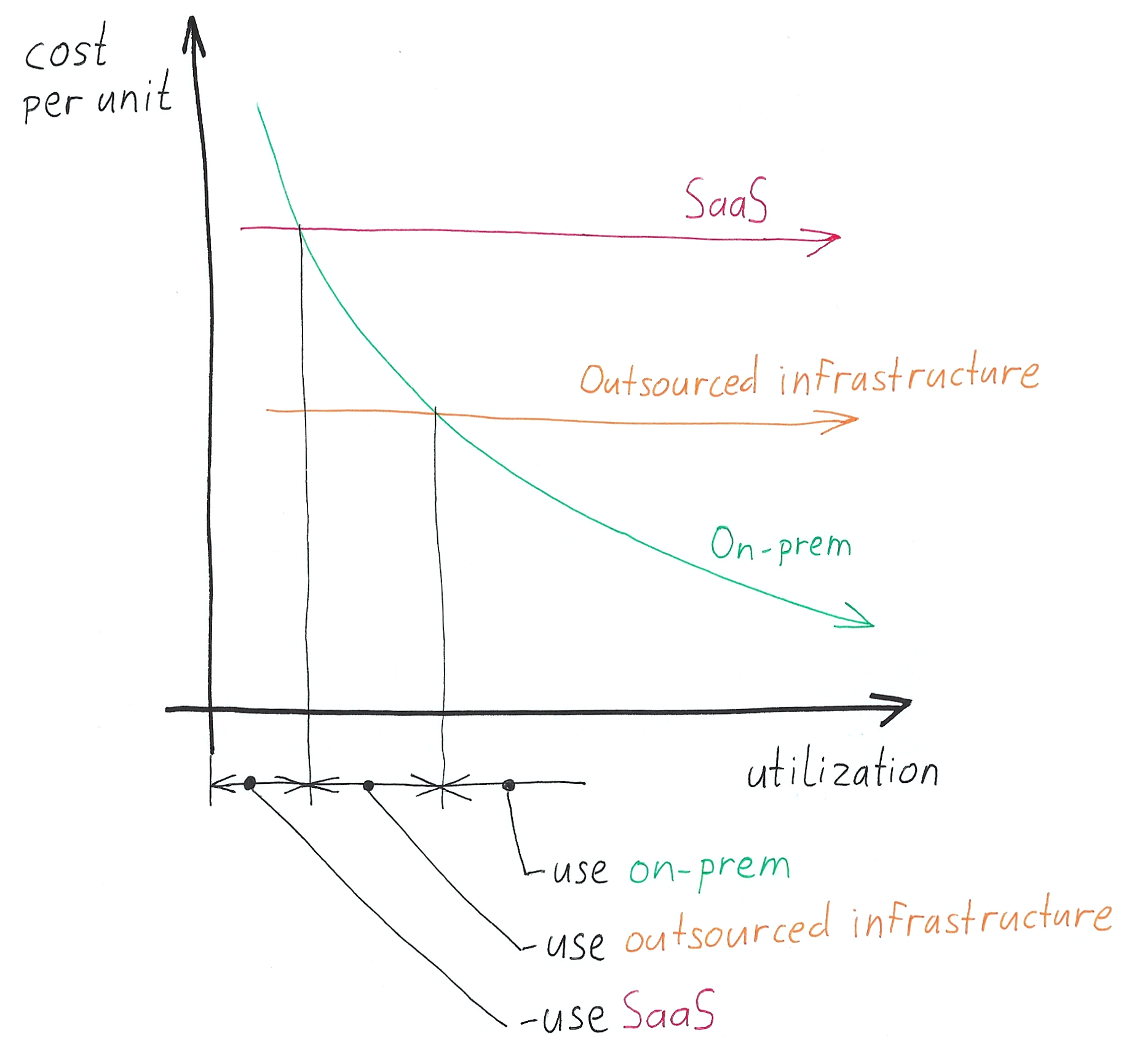
The lines in the diagram above will look different for each application, based on the differences in fixed and variable costs for each approach. As a generalization, and presuming you have a choice, on-premise deployments would typically be most cost-effective for applications that are highly-utilized and SaaS for those with low utilization.
What is the risk?
Let’s look closer at who can “pull the plug”. The risk is cumulative. For example, if you’re using a SaaS application, then both the risks under your control and the risks under the infrastructure provider’s control need to be accounted for in the SaaS category.
The graphic below illustrates some of the relevant risks.
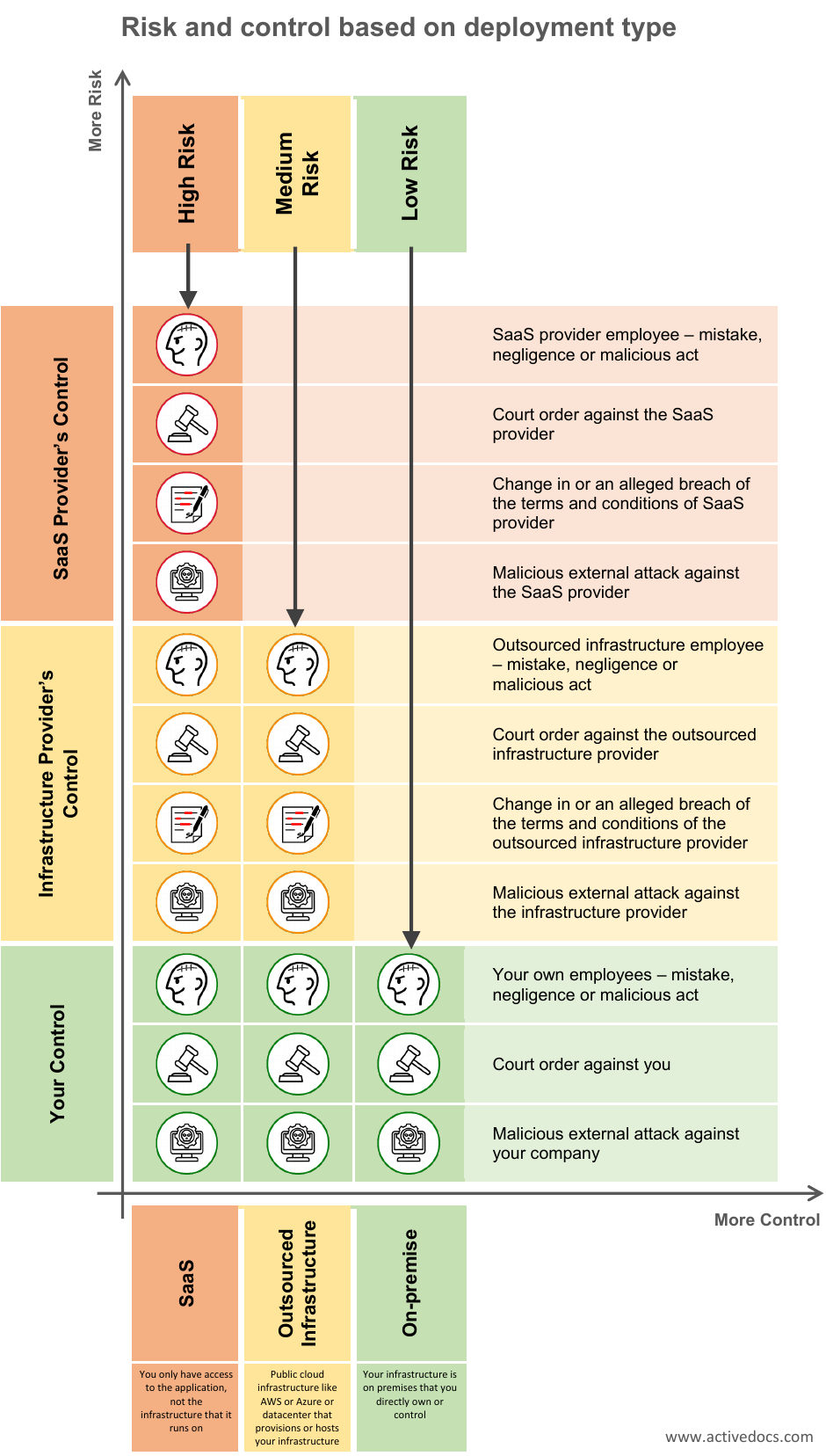
The degree of risk is different for each type of deployment.
What is the right deployment type for your application and your business?
There is no single magic formula. Often, the available approaches may be dictated by legislation or industry regulations for data handling. If you have the freedom of choice, then consider criticality of the application and the available resources. What is the impact if the application is offline for a prolonged period of time? What is your disaster recovery plan? Does it take into consideration the risks outlined in the table above? For example, if your outsourced infrastructure provider cuts you off because of an alleged breach of terms and conditions, then it won’t matter that you have your apps running on servers in multiple geographical locations.
What do our clients choose?
Our client base primarily consists of multi-national or large national organizations. For these organizations, their documents are their business. It means that their documents are the key to their revenue generation and regulatory compliance. This tends to bias them towards the category where they need a high degree of control and can justify the expense associated with owning and controlling their own infrastructure. However, it doesn’t mean that all their applications are deployed “on-premise”.
They carefully weigh the criticality, utilization, and the nature of use of each type of application and choose the option that is the best fit for them.
The key question to ask is:
What will be the risk and cost to the business if someone inadvertantly pulls the plug on this application?
Martin Srubar
Senior Technology Evangelist
Martin’s engineering background and his passion for great products whether in physical or software form are complemented by his understanding of ActiveDocs applications and how they meet the requirements and fit the architecture of the company’s clients. Martin continues to engage with potential and existing customers, adding market intelligence and customer feedback into the company’s ongoing product development strategy.
